Stop SMS pumping. Start
SMS pumping is draining millions from digital marketplace platforms every year. Prove’s Unified Authentication solution cuts authentication costs by up to 50% - and shuts the door on fraudulent traffic.
Trusted by 1,000+ companies globally







reduction in SMS volume
reduction in auth costs
Global SMS protection
Confidently verify consumers at onboarding and through the
customer lifecycle. Pre-populate application forms with verified identity information, reducing consumer friction and fraud.
Prove verifies various personal information elements, while also risk scoring in real-time. This provides an unparalleled identity verification solution that adapts to evolving threats.
Enjoy fast, easy, and secure authentication. Leverage passwordless and OTP-less authentication for mobile apps, web-based, and omni-channel experiences.
Scale customer loyalty and give users peace of mind. Increase platform trust with verified identities and stop impersonators, fraudsters, bots, and scams.

SMS Pumping is a growing problem - and
your auth bill is a target
SMS pumping artificially inflates OTP traffic by exploiting verification flows.
For digital marketplace platforms with high user volumes, the financial damage adds up fast.
Fraudsters trigger high volumes of one-time passcodes (OTPs), driving up SMS spend without generating legitimate customer activity.
Automated bots continuously request OTPs, exploiting open or unprotected verification endpoints.
SMS pumping schemes are often tied to premium-rate numbers or revenue-sharing models, turning your authentication flow into a profit engine for attackers
Weak OTP controls make it easier for attackers to probe systems, test phone numbers, and identify vulnerabilities.
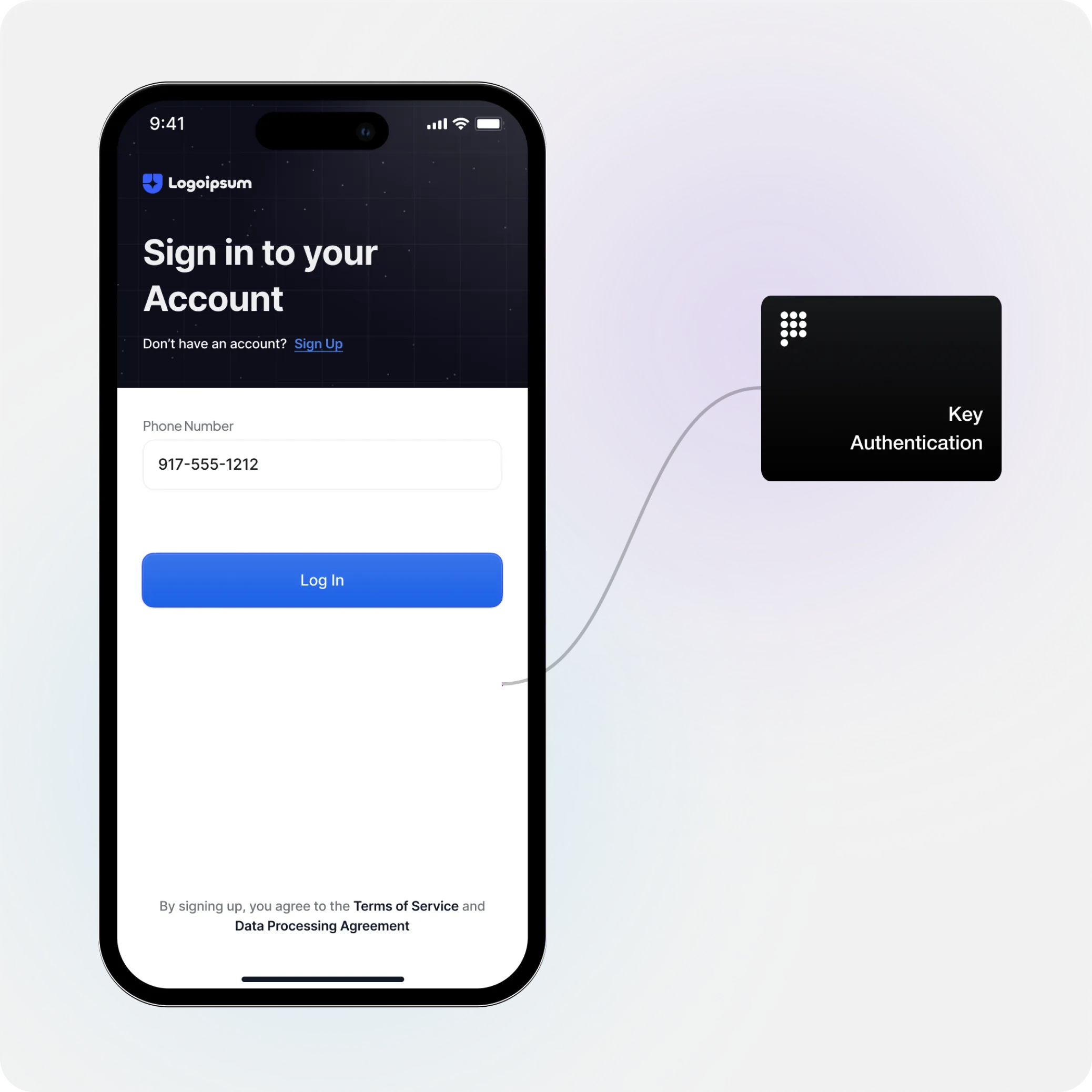
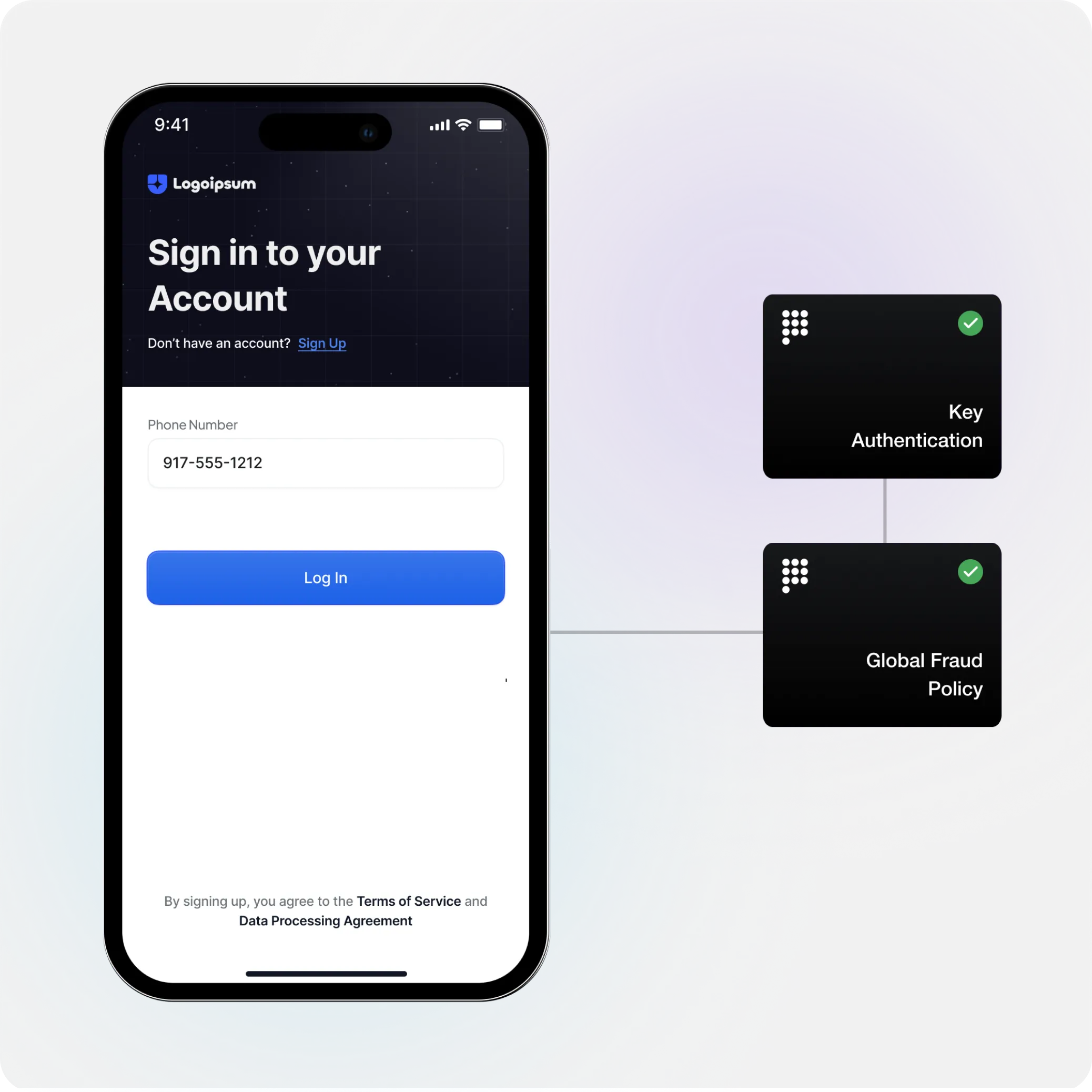
How Unified Authentication Works
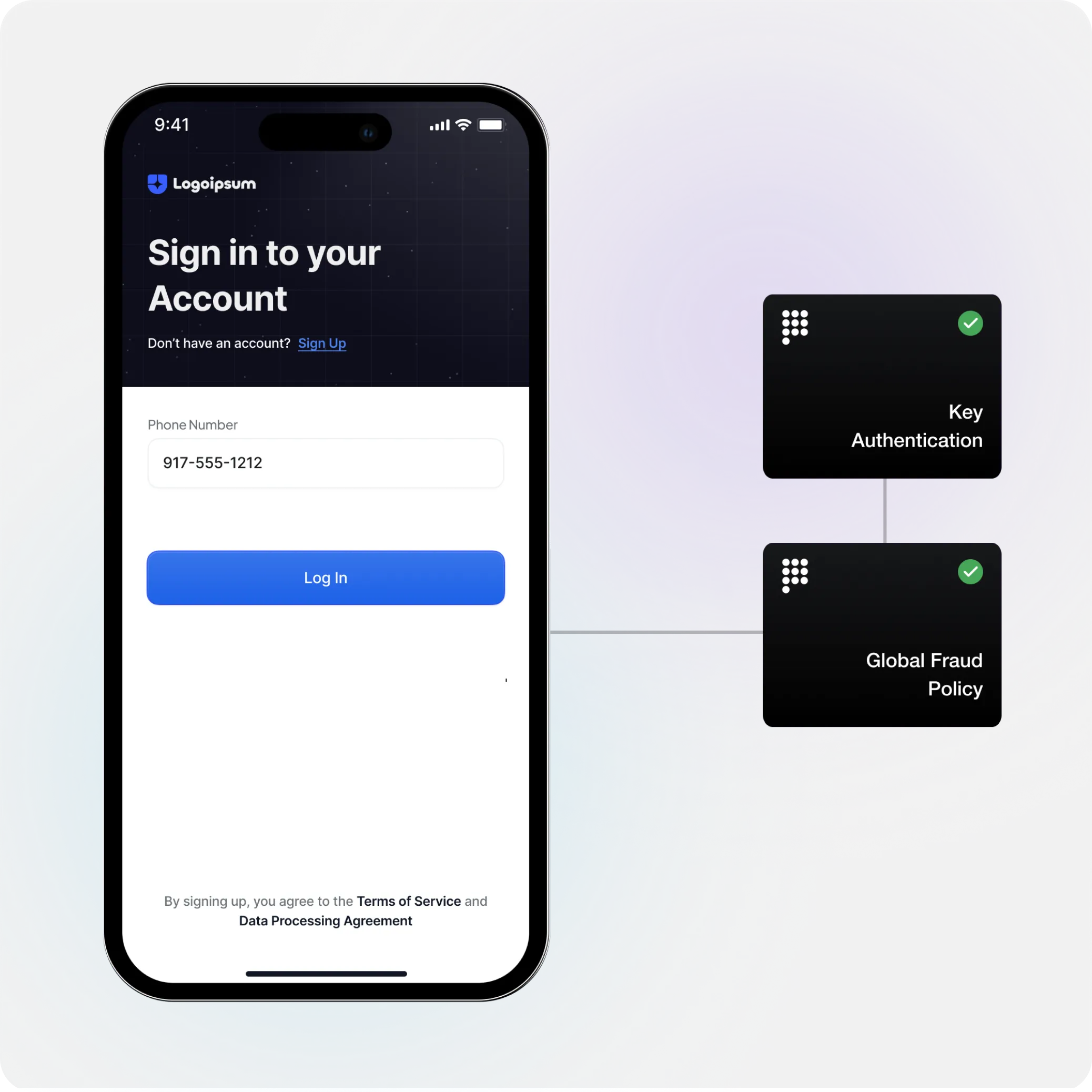
Upgrade your authentication stack with passive, persistent verification that eliminates clunky
OTPs and seamlessly recognizes returning users across sessions, devices, and lifecycle changes, without added friction.
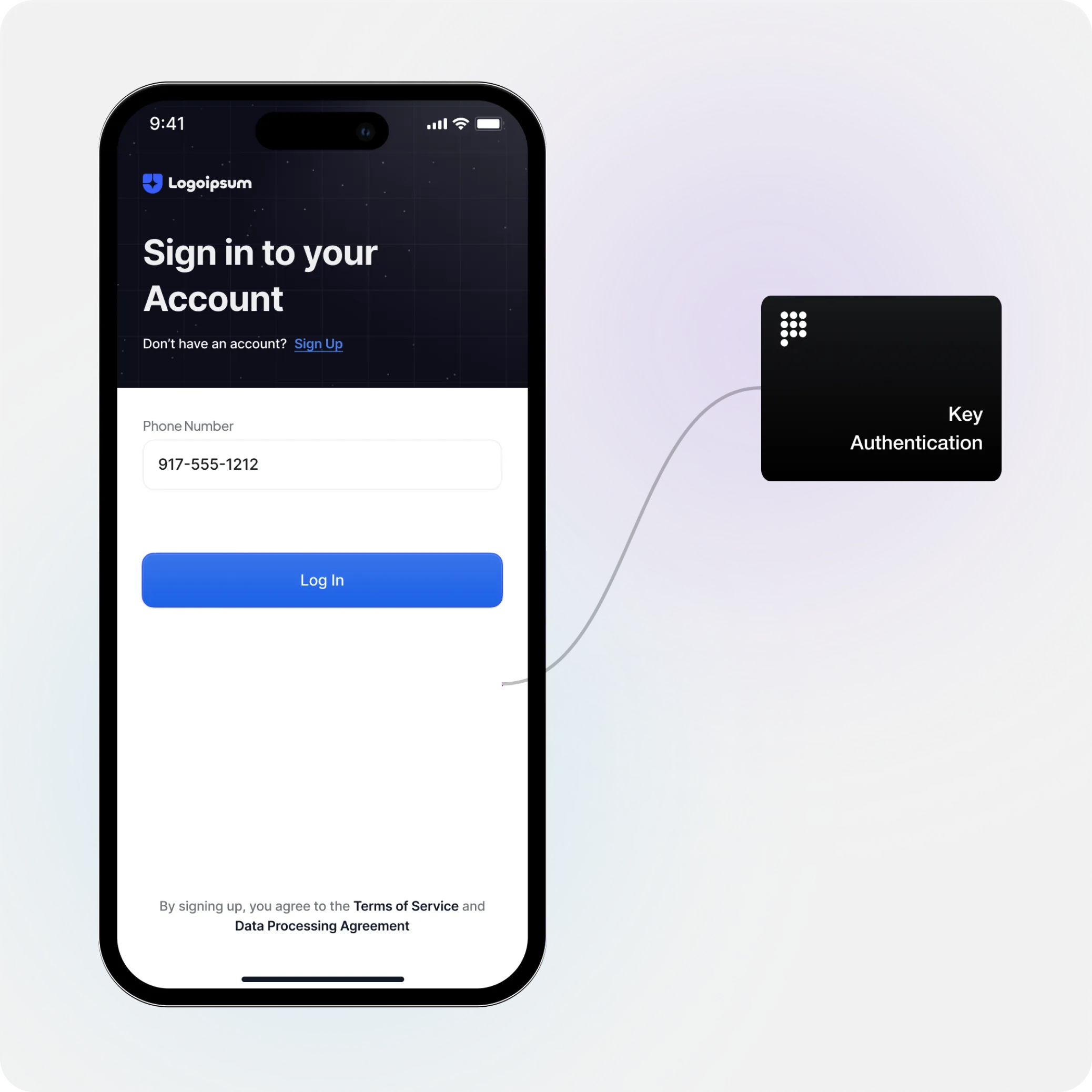
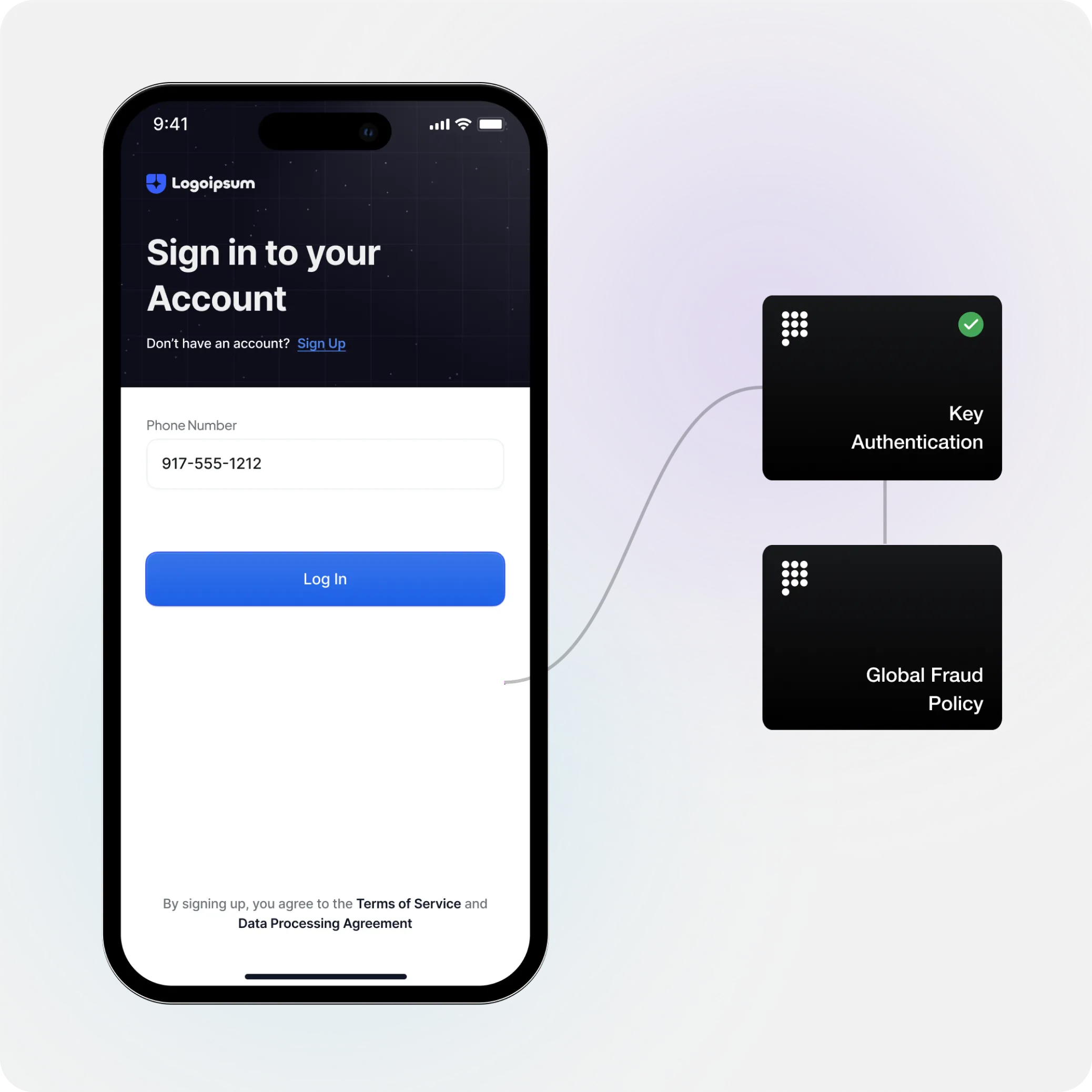
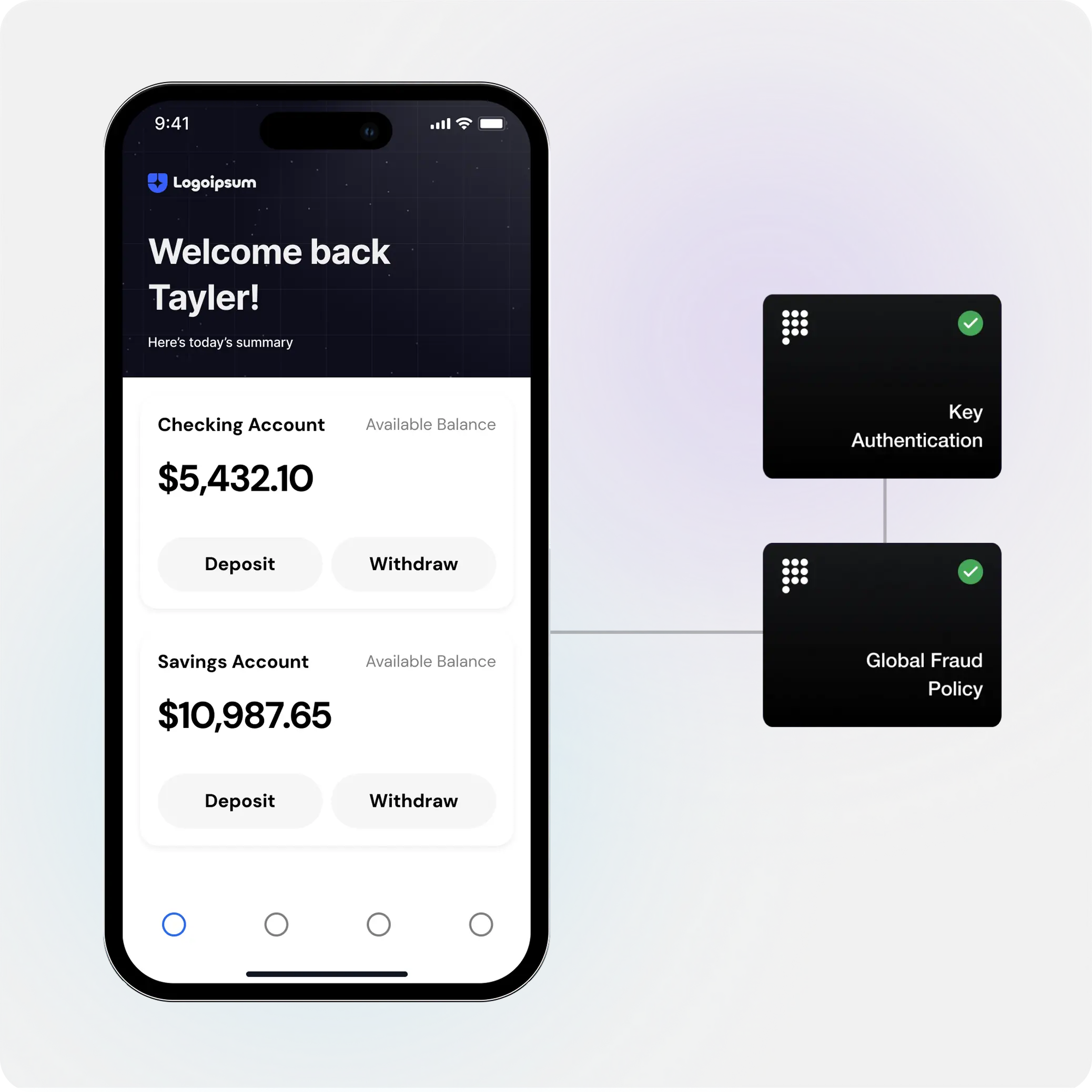
A returning user on a recognized device attempts an action requiring authentication (like logging in or validating a high-risk transaction).
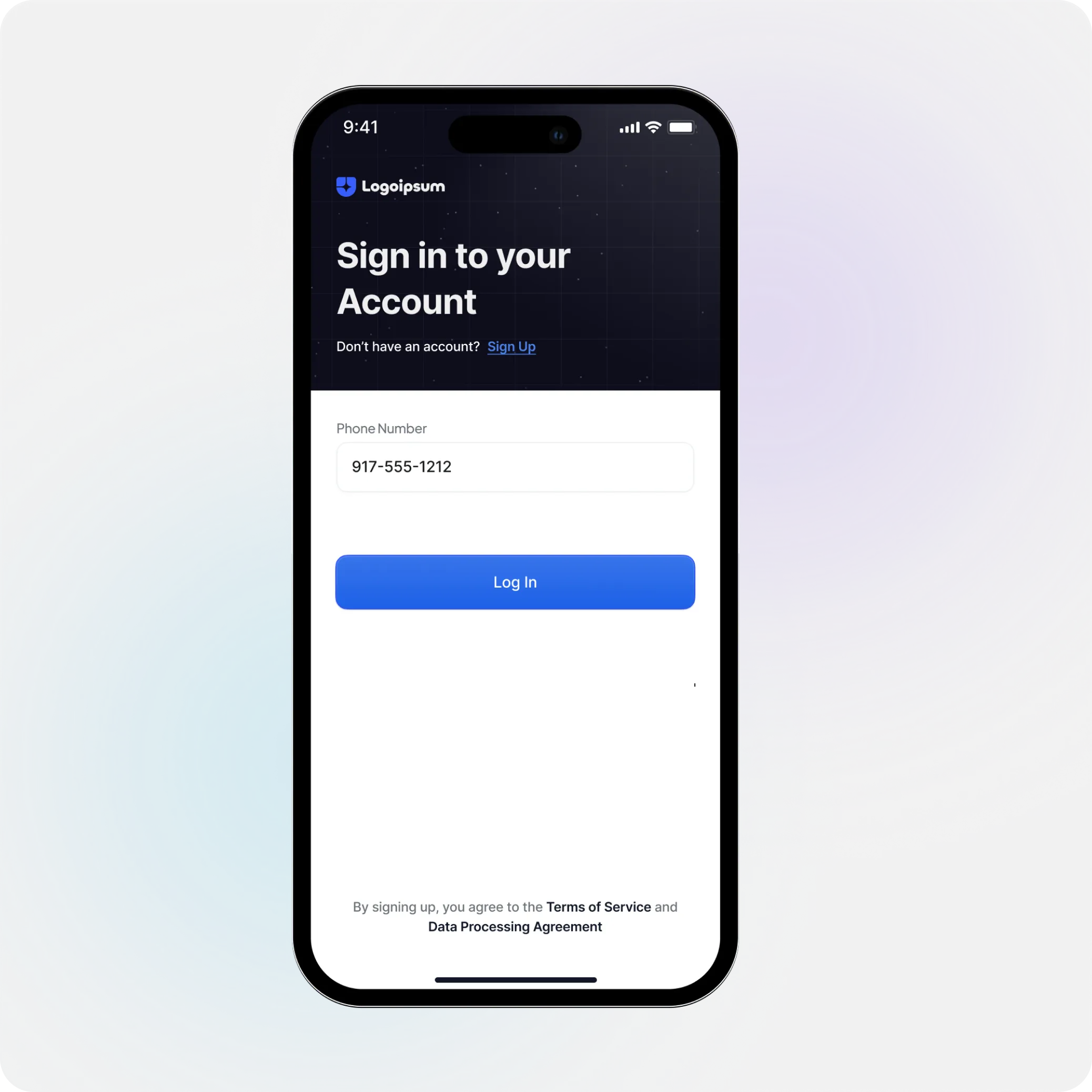
Prove first attempts passive authentication, like Prove's Prove Key and Mobile Auth, and silently verifying the device with a cryptographic key or sim validation.
Rather than a stack of unlinked and often conflicting data signals, Prove’s Global Fraud Policy applies all Prove learnings on fraud trends, alerts, and nuanced data attributes into a unified, intelligent output, detailing the specific reason codes customers need for comprehensive risk management.
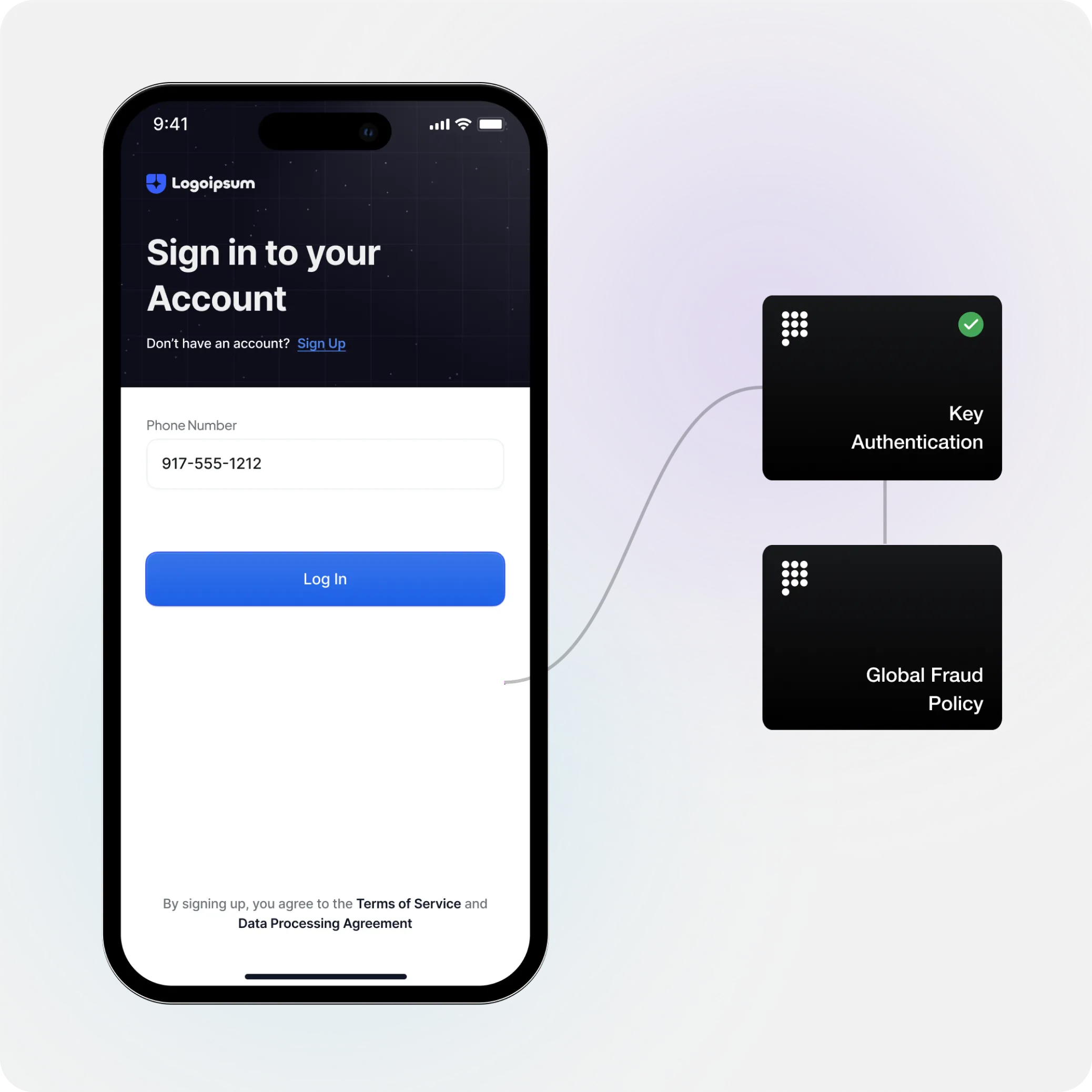
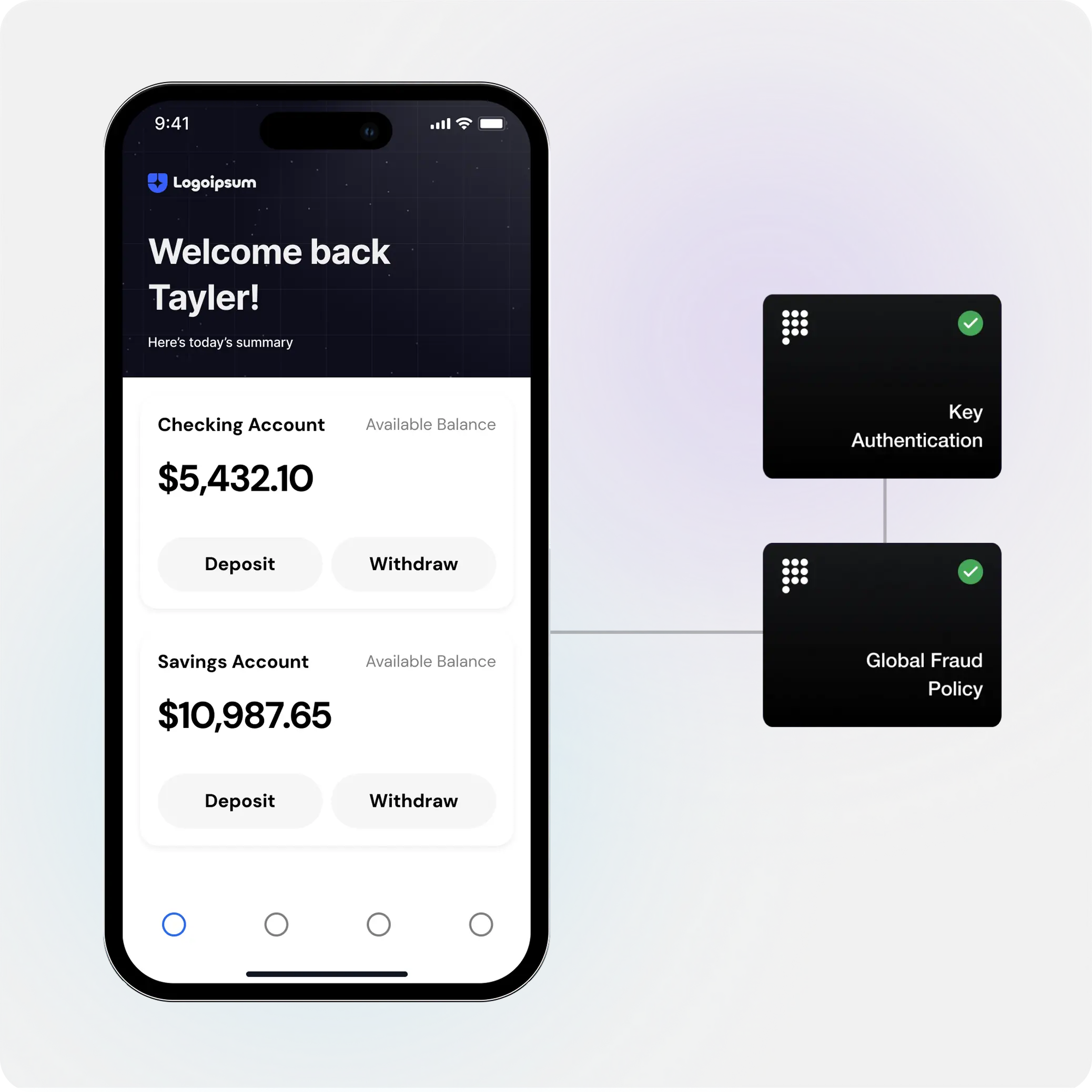
Prove returns a success or failure response, allowing the transaction to proceed or be blocked/reviewed.
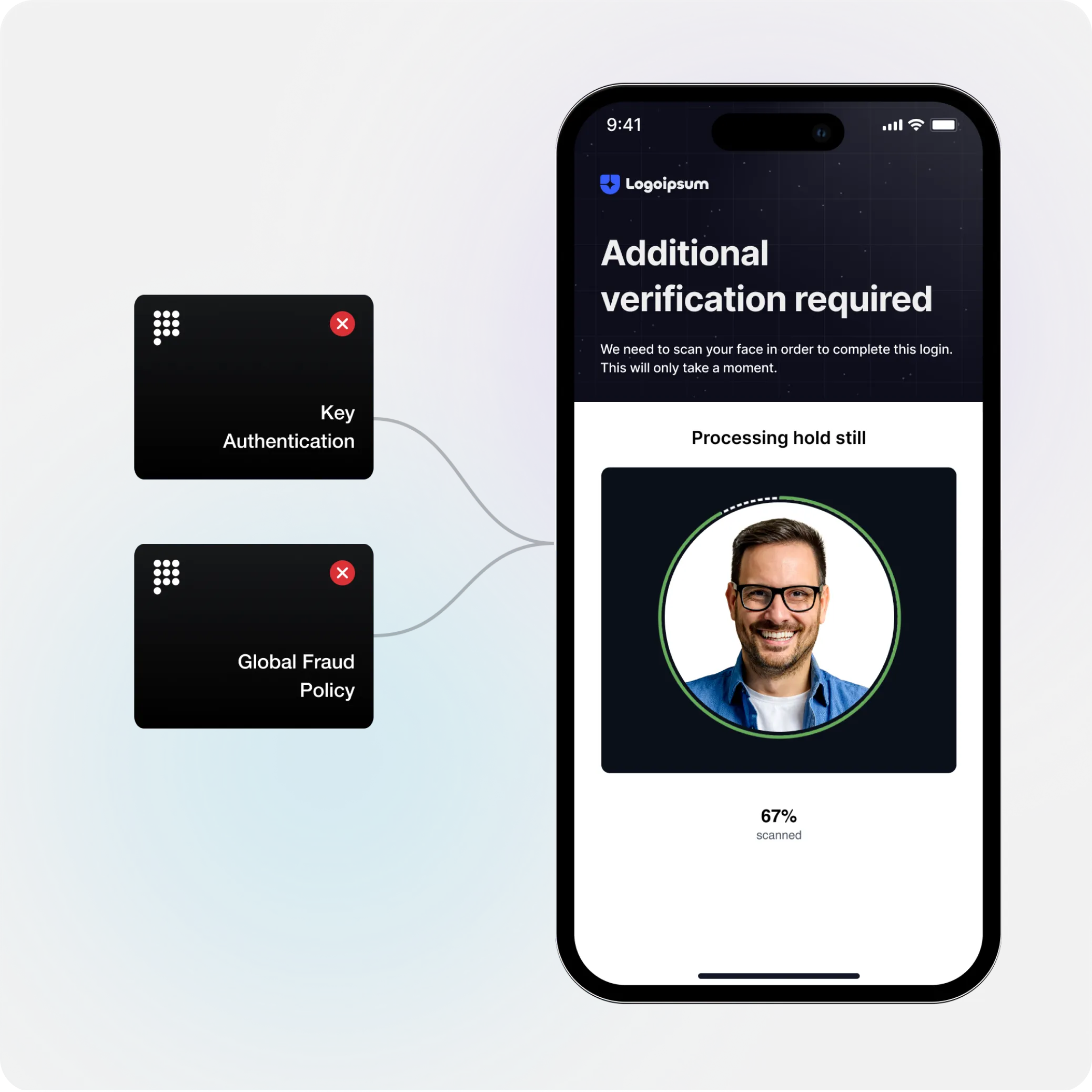
If a key cannot be validated, Prove will waterfall to alternative authentication methods.
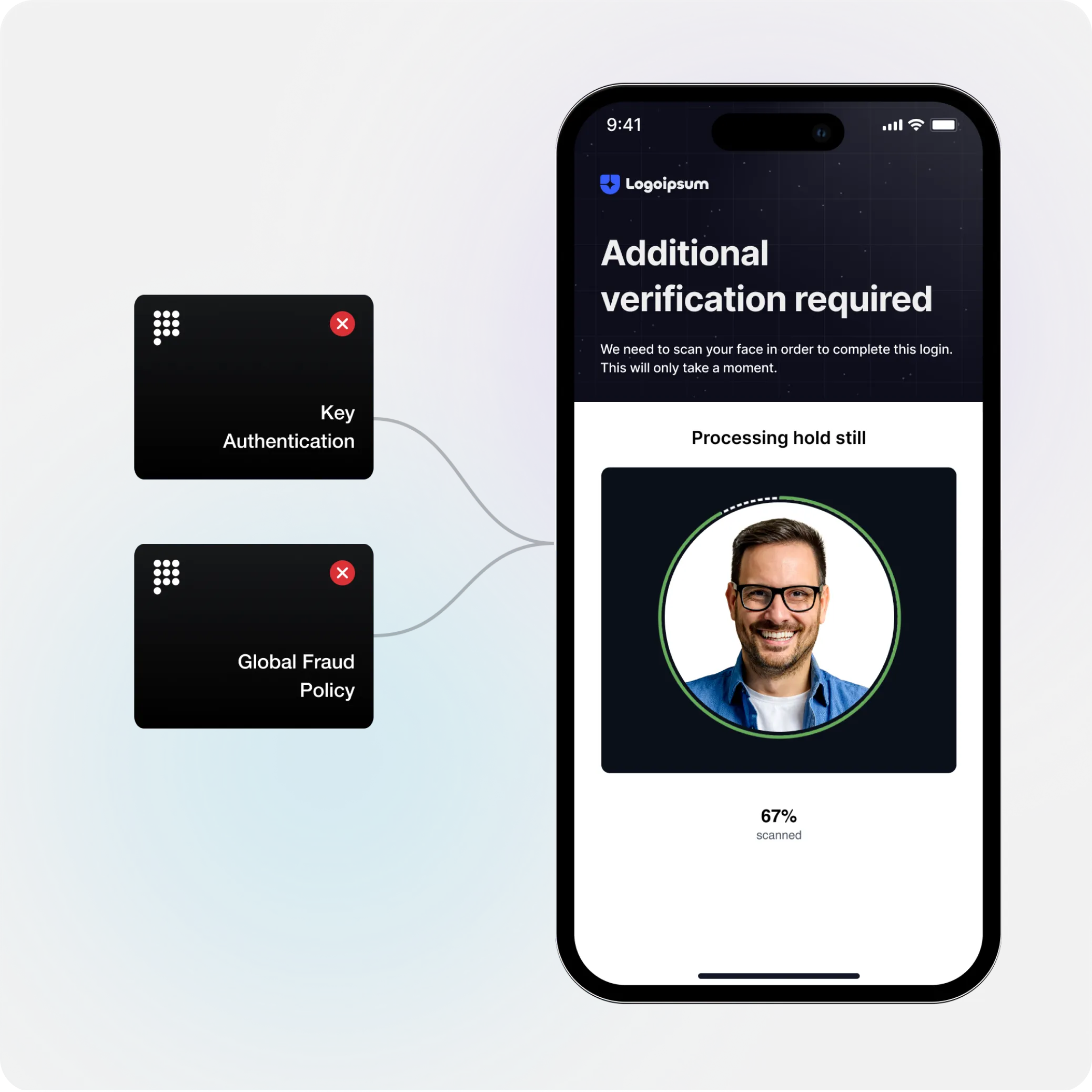
If step-up was required, we will bind a key to the users device after successfully logging in. This will allow for a seamless login next time.
What Customers Say:
“Since implementing identity verification with Prove, we’ve seen measurable improvements across our north star metrics, including fewer member closures and a reduced impact rate—lowering member exposure to messages from untrusted accounts.”