The Last Gap in Silent Network Authentication. Closed.

For many years, legacy identity verification methods have relied on a familiar, but increasingly outdated method: the SMS one-time passcode (OTP). Whether logging into a bank account or confirming a transaction, users receive a code via text and enter it to prove who they are. It's never been elegant, but for many years it was adequate to meet a need.
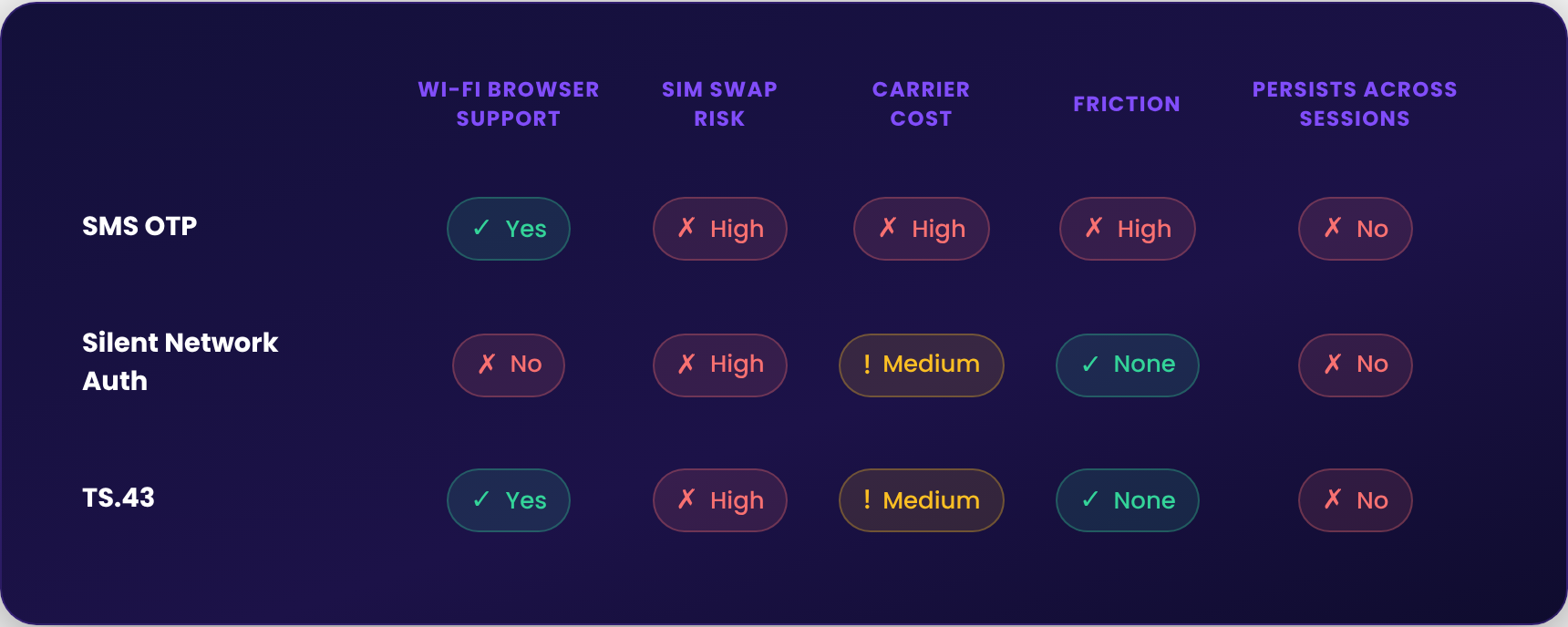
But the nature of risk has changed. A lot. Regulators around the globe are phasing out SMS-based authentication for high-risk financial services because of concerns about fraud, SIM swaps, and phishing attacks. As a result, the industry has been looking for a stronger, more seamless way to verify identity.
What Is TS.43 and What Does It Solve?
GSMA TS.43 Release 11 is a new standard that extends SIM and eSIM-based authentication across any network type, with consent-based access for third-party apps and services. For identity, that extension matters.
Silent network authentication (SNA) has always had a hard limit. It works in apps on cellular or Wi-Fi, but the moment a user switches to a browser on Wi-Fi, it fails. For many enterprises that's not an edge case, it's a significant share of sessions. TS.43 closes that gap by moving authentication to the SIM card itself, cryptographic, hardware-backed, independent of connection type. Everywhere SNA already works, plus the one place it never could: a browser on Wi-Fi.
That matters. But it's worth understanding why carriers are pushing it.
SMS OTP is a roughly $10 billion annual business for mobile operators, under pressure from fraud, regulation, and enterprise migration toward passkeys and app-based flows. Estimates suggest a quarter of that revenue is tied to fraudulent traffic. TS.43 is carriers' answer: modernize authentication, defend their role in the identity stack, replace declining OTP revenue with a new transaction type. Enterprises should expect pricing comparable to what they pay for OTP today. This is a business move as much as a technical one.
And it still has two unresolved problems. First, SIM swap. TS.43 authenticates the SIM, not the person. Swap the SIM and you've defeated it, the same root vulnerability that made OTP untenable. Second, cost and complexity. TS.43 is still a carrier transaction, the spend changes shape, it doesn't disappear.
How Prove Is Building TS.43 Into Its Platform
Prove is integrating TS.43 into Prove Mobile Auth and Prove Unified Authentication solutions. Existing clients won't change a thing, no new carrier contracts, no integration project, no OEM certification cycles. It will simply be available, rolling out globally as carrier infrastructure matures.
There is one area that requires care. TS.43 mandates carrier by carrier end user consent. Done poorly, a clunky or confusing consent experience will erode consumer trust and kill conversion before authentication even runs. Prove manages that consent layer on behalf of clients, handling the variation across carriers, markets, and regulatory requirements so the experience stays seamless and adoption stays high.
TS.43 is a better signal. The Prove Key is where identity lives.
Once identity is established, using TS.43, OTP, or whatever the user consents to, we bind it to the device cryptographically. Not the SIM. The device. Rooted in years of longitudinal signals that no session level credential can replicate. A SIM swap doesn't touch it. And because trust persists across sessions, the carrier transaction doesn't repeat. Clients on Prove's platform have cut SMS OTP costs by 50% without touching their security posture.
Extending SNA Beyond Its Legacy Limits
Prove's north star is simple: a world where consumers never have to think about security. No codes. No friction. No vulnerability. Just persistent, always-on identity that works in the background, so every digital transaction is protected without the person ever knowing it happened.
Every capability we add moves us closer to that. The latest is closing the last gap in silent network authentication.
That limit is now gone.
TS.43 brings silent, cryptographic, hardware-backed authentication to every session, regardless of how the device connects. Browser or app. Cellular or Wi-Fi. It works everywhere SNA already does, plus the one place it never could.
And two problems remain unresolved. First, SIM swap. The new standard authenticates the SIM, not the person. Swap the SIM and you've defeated it, the same root vulnerability that made OTP untenable. Second, cost. It's still a carrier transaction. The spend changes shape, it doesn't disappear.

Every new standard gets evaluated the same way: does it improve experience, reduce fraud, lower cost, simultaneously, without sacrifice? TS.43 earns its place. Prove makes it better.
TS.43 verifies the SIM. Prove verifies the person, with years of longitudinal identity signals behind every answer. That's the difference between a check and a conviction.

Keep reading
 Read the article: Identity Is the Growth Engine for Digital Marketplaces
Read the article: Identity Is the Growth Engine for Digital MarketplacesDigital marketplaces depend on trust to drive growth, reduce fraud, and improve user experiences. This blog explores how modern identity verification and phone-centric identity intelligence help marketplaces increase conversion, prevent account abuse, and scale globally with confidence.
 Read the article: FIDO's Agentic Commerce Blueprint Is a Major Step Forward. Here's What Comes Next.
Read the article: FIDO's Agentic Commerce Blueprint Is a Major Step Forward. Here's What Comes Next.The FIDO Alliance’s new standards for agentic commerce mark a major step toward trusted AI-driven transactions, but they leave a critical question unanswered: how to verify the real identities behind AI agents. This article explores the gaps in AP2 and Verifiable Intent (VI) protocols and why foundational identity infrastructure will determine whether agentic commerce can scale securely.
 Read the article: Prove and Velocity Partner to Close the Trust Gap in the Global Stablecoin Economy
Read the article: Prove and Velocity Partner to Close the Trust Gap in the Global Stablecoin EconomyProve and Velocity have partnered to bring trusted identity verification to the global stablecoin economy, helping enterprises, banks, and payment providers enable secure, compliant cross-border payments and treasury operations.













